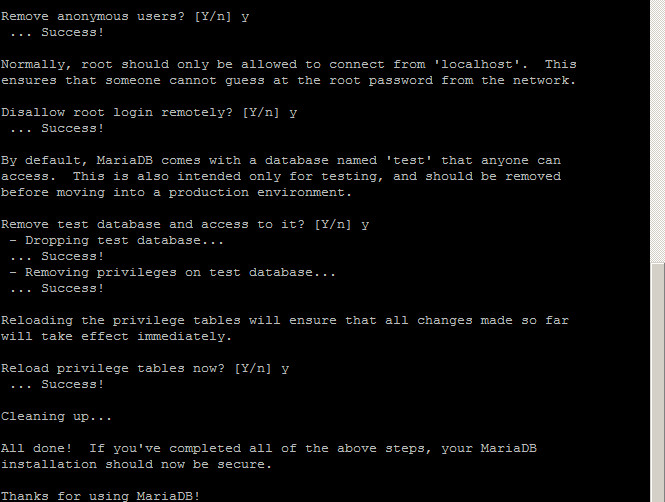
mysql_secure_installation – MySQL Script
mysql_secure_installation – MySQL Script mysql_secure_installation is a shell script available on Unix systems, and enables you to improve the security of your MariaDB or MySQL installation in the following ways: You can set a password for root accounts. You can remove root accounts that are accessible from outside the local host. You can remove anonymous-user accounts. … Read more