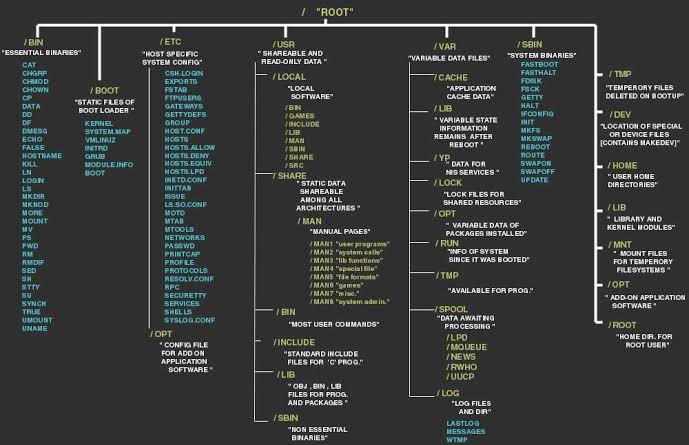
the Linux file tree
This post takes a look at the most common directories in the Linux file tree. It also shows that on Unix everything is a file. filesystem hierarchy standard Many Linux distributions partially follow the Filesystem Hierarchy Standard. The FHS may help make more Unix/Linux file system trees conform better in the future. The FHS is … Read more