How to Create/Add Users in Jenkins and Manage Permissions
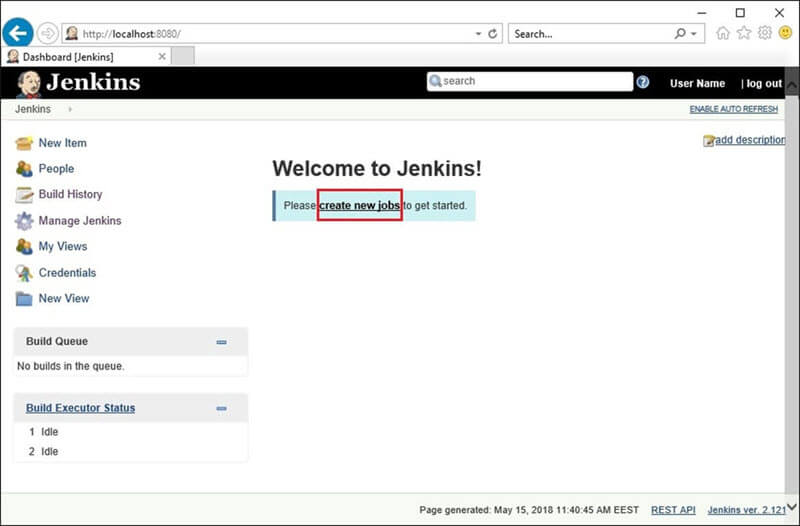
Today, We will know how to create or add new users in Jenkins and How to manage Permissions in Jenkins. Generally, in a large organization, there are multiple, separate teams to manage and run jobs in Jenkins. But managing this crowd of users and assigning roles to them can prove troublesome. Read: How to Integrate … Read more