Applications often implement “remember me” functions as a convenience to users, to prevent them needing to reenter their username and password each time they use the application from a specific computer. These functions are often insecure by design and leave the user exposed to attack both locally and by users on other computers:
■ Some “remember me” functions are implemented using a simple persistent cookie, such as RememberUser=peterwiener. When this cookie is submitted to the initial application page, the application trusts the cookie to authenticate the user, and creates an application session for that person, bypassing the login. An attacker can use a list of common or enumerated usernames to gain full access to the application without any authentication.
■ Some “remember me” functions set a cookie which does not contain the username but rather a kind of persistent session identifier — for example, RememberUser=1328 . When the identifier is submitted to the login page, the application looks up the user associated with it and creates an application session for that user. As with ordinary session tokens, if the session identifiers of other users can be predicted or extrapolated, an attacker can iterate through a large number of potential identifiers to find those associated with application users, and so gain access to their accounts without authentication.
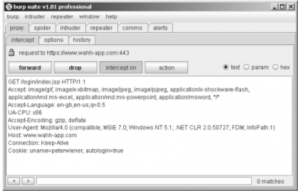
Figure -1: A vulnerable “remember me” function
■ Even if the information stored in a cookie for re-identifying users is suitably protected (e.g., encrypted) to prevent other users from determining or guessing it, the information may still be vulnerable to capture through a bug such as cross-site scripting.
NEXT is..User Impersonation Functionality……………,.,.,.,.,.,.,.,.,