WHAT IS CYBER LAW?
Cyber Law is the law governing cyber space. Cyber space is a very wide term and includes computers, networks, software, data storage devices (such as hard disks, USB disks etc), the Internet, websites, emails and even electronic devices such as cell phones, ATM machines etc. It focuses on enhancing a jurisdiction‘s legal system by establishing laws that reflect and deal with the technological changes that permeate society and describes the legal issues related to use of inter-networked information technology.
Cyber law encompasses laws relating to:
- Cyber Crimes
- Electronic and Digital Signatures
- Intellectual Property
- Data Protection and Privacy
Cyber crimes are unlawful acts where the computer is used either as a tool or a target or both. The enormous growth in electronic commerce (e-commerce) and online share trading has led to a phenomenal spurt in incidents of cyber crime.
Electronic signatures are used to authenticate electronic records. Digital signatures are one type of electronic signature. Digital signatures satisfy three major legal requirements–signer authentication, message authentication and message integrity. The technology and efficiency of digital signatures makes them more trustworthy than hand written signatures.
Intellectual property is refers to creations of the human mind e.g. a story, a song, a painting, a design etc. The facets of intellectual property that relate to cyber space are covered by cyber law.
These include:
- Copyright law in relation to computer software, computer source code, websites, cell phone content etc,
- Software and source code licenses
- Trademark law with relation to domain names, meta tags, mirroring, framing, linking etc
- Semiconductor law which relates to the protection of semiconductor integrated circuits design and layouts,
- Patent law in relation to computer hardware and software.
Data protection and privacy laws aim to achieve a fair balance between the privacy rights of the individual and the interests of data controllers such as banks, hospitals, email service providers etc. These laws seek to address the challenges to privacy caused by collecting, storing and transmitting data using new technologies.
NEED FOR CYBER LAW-
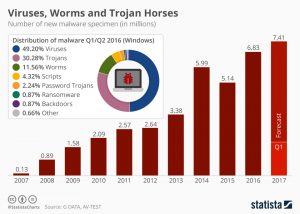
In Indian law, cyber crime has to be voluntary and willful, an act or omission that adversely affects a person or property. The cyber laws provide the backbone for e-commerce and India‘s approach has been to look at e-governance and e-commerce primarily from the promotional aspects looking at the vast opportunities and the need to sensitize the population to the possibilities of the information age. There is the need to take in to consideration the security aspects. The latest statics also shows the steep increase in various types of cyber crime and abuses during 2007 and 2017.
There are various reasons why it is extremely difficult for conventional law to cope with cyberspace. Some of these are discussed below:
1. Cyberspace is an intangible dimension that is impossible to govern and regulate using conventional law.
2. Cyberspace has complete disrespect for jurisdictional boundaries. A person in India could break into a bank‘s electronic vault hosted on a computer in USA and transfer millions of Rupees to another bank in Switzerland, all within minutes. All he would need is a laptop computer and a cell phone.
3. Cyberspace handles gigantic traffic volumes every second. Billions of emails are crisscrossing the globe even as we read this, millions of websites are being accessed every minute and billions of dollars are electronically transferred around the world by banks every day.
4. Cyberspace is absolutely open to participation by all. A ten year- old in Bhutan can have a live chat session with an eight year-old in Bali without any regard for the distance or the anonymity between them.
5. Cyberspace offers enormous potential for anonymity to its members. Readily available encryption software and steganographic tools that seamlessly hide information within image and sound files ensure the confidentiality of information exchanged between cyber-citizens.
6. Cyberspace offers never-seen-before economic efficiency. Billions of dollars worth of software can be traded over the Internet without the need for any government licenses,
shipping and handling charges and without paying any customs duty.
7. Electronic information has become the main object of cyber crime. It is characterized by extreme mobility, which exceeds by far the mobility of persons, goods or other services. International computer networks can transfer huge amounts of data around the globe in a matter of seconds.
8. A software source code worth crores of rupees or a movie can be pirated across the globe within hours of their release.
9. Theft of corporeal information (e.g. books, papers, CD ROMs, floppy disks) is easily covered by traditional penal provisions.
However, the problem begins when electronic records are copied quickly, inconspicuously and often via telecommunication facilities. Here the ―original information, so to say, remains in the possession of the owner and yet information gets stolen.
CYBER LAWS: INTERNATIONAL PERSPECTIVE
Cyber crime is a worldwide faced threat which is dealt with various cyber laws made universally by different territories as cyber crime spans not only state but national boundaries as well. So let us know look into the international perspectives of Cyber Laws. A single transaction may involve the laws of at least three jurisdictions:
- The laws of the state/nation in which the user resides.
- The laws of the state/nation that apply where the server hosting the transaction is located,
- The laws of the state/nation which apply to the person or business with whom the transaction takes place.
At the Tenth United Nations Congress on the Prevention of Crime and Treatment of Offenders, in a workshop devoted to the issues of crimes related to computer networks, cyber crime was broken into two categories and defined thus:
a. Cyber crime in a narrow sense (computer crime): Any illegal behavior directed by means of electronic operations that targets the security of computer systems and the data processed by them.
b. Cyber crime in a broader sense (computer-related crime): Any illegal behavior committed by means of, or in relation to, a computer system or network, including such crimes as illegal possession [and] offering or distributing information by means of a computer system or network.
Of course, these definitions are complicated by the fact that an act may be illegal in one nation but not in another.
There are more concrete examples, including
- Unauthorized access.
- Damage to computer data or programs
- Computer sabotage
- Unauthorized interception of communications
- Computer espionage
So a user in one of the United States conducting a transaction with another user in Britain through a server in Canada could theoretically be subject to the laws of all three countries as they relate to the transaction at hand. While there is some United States law that does restrict access to materials on the internet, it does not truly filter the internet. Many Asian and Middle Eastern nations use any number of combinations of code-based regulation (one of Lessig’s four methods of net regulation) to block material that their governments have deemed inappropriate for their citizens to view. China and Saudi Arabia are two excellent examples of nations that have achieved high degrees of success in regulating their citizens‘ access to the internet.
In United States,
USDOJ: United States Department of Justice works on the mission to enforce the law and defend the interests of the United States; to ensure public safety against threats foreign and domestic; to provide federal leadership in preventing and controlling crime; to seek just punishment for thoseguilty of unlawful behavior; and to ensure fair and impartial administration of justice for all Americans. The department is committed to develop fair and just punishment for crimes committed in the future.
Securely Protect Yourself against Cyber Trespass Act (SPY ACT)
Says: It is unlawful for any person, who is not the owner or authorized user of a protected computer, to engage in unfair or deceptive acts or practices that involve any conduct with respect to the protected computer, Modifying settings related to use of the computer or to the computer’s access to or use of the Internet by altering of any kind, Collecting personally identifiable information through the use of a keystroke logging function or Inducing the owner or authorized user of the computer to disclose personally identifiable information by means of a Web page. From Legal Perspective, there is U.S. Federal Law having following sections describing the laws and penalties:
Federal Criminal Code Related to Computer Crime:
- 18 U.S.C. § 1029. Fraud and Related Activity in Connection with Access Devices
- 18 U.S.C. § 1030. Fraud and Related Activity in Connection with Computers
- 18 U.S.C. § 1362. Communication Lines, Stations, or Systems
- 18 U.S.C. § 2510 et seq. Wire and Electronic Communications Interception and Interception of Oral Communications
- 18 U.S.C. § 2701 et seq. Stored Wire and Electronic Communications and Transactional Records Access.
In Mexico,
There is a law for Unauthorized computer use:-
A person who knowingly, willfully and without authorization, or having obtained authorization, uses the opportunity the authorization provides for purposes to which the authorization does not extend, directly or indirectly accesses, uses, takes, transfers, conceals, obtains, copies or retains possession of any computer, computer network, computer property, computer service, computer system or any part thereof, when the:
- damage to the computer property or computer service has a value of two hundred fifty dollars ($250) or less, is guilty of a petty misdemeanor;
- damage to the computer property or computer service has a value of more than two hundred fifty dollars ($250) but not more than five hundred dollars ($500), is guilty of a misdemeanor; damage to the computer property or computer service has a value of more than five hundred dollars
- ($500) but not more than two thousand five hundred dollars ($2,500), is guilty of a fourth degree felony;
- damage to the computer property or computer service has a value of more than two thousand five hundred dollars ($2,500) but not more than twenty thousand dollars ($20,000), is guilty of a third degree felony;
- damage to the computer property or computer service has a value of more than twenty thousand dollars ($20,000), is guilty of a second degree felony.
In Brazil,
There are laws defined under cyber laws. Brazilian Laws states:
- ENTRY OF FALSE DATA INTO THE INFORMATION SYSTEM: Penalty-imprisonment for 2 to 12 years, and fines
- UNAUTHORIZED MODIFICATION OR ALTERATION OF THE INFORMATION SYSTEM: Penalty-detention for 3 months to 2 years, and fines.
In Canada,
Canadian Criminal Code Section 342.1 states:
Everyone who, fraudulently and without color of right,
a) Obtains, directly or indirectly, any computer service,
b) By means of an electro-magnetic, acoustic, mechanical or other device, intercepts or causes to be intercepted, directly or indirectly, any function of a computer system.
c) Uses or causes to be used, directly or indirectly, a computer system with intent to commit an offence under paragraph (a) or (b) or an offence under section 430 in relation to data or a computer system.
Person to commit an offence under paragraph (a), (b) or (c) is guilty of an indictable offence and liable to imprisonment for a term not exceeding ten years.
E-GOVERNANCE
“E-governance is the use of ICT by different actors of the society with the aim to improve their
access to information and to build their capacities.”
E-commerce is fundamentally different from the conventional commercial transactions based on face-to-face interaction and document exchange. As e-commerce spreads rapidly, nations began to review the methodology, practices and rules applicable in conventional transactions and are focusing on readjusting their legal settings to create an environment more conducive to e- commerce.
It is the public sector‘s use of information and communication technologies with the aim of improving information and service delivery, encouraging citizen participation in the decision- making process and making government more accountable, transparent and effective. Governance is an interaction between the Government and the Governed. It implies administration through its Machinery in accordance with laws and established procedures.
E-Governance implies Governance employing Information Technology in administration (viz. for collection of information, its processing, providing information in prescribed format & and using them for decision making etc.)
RELEVANT LAWS
India became independent on 15th August, 1947. Since then it has been struggling through to make its stand in the world. Many new technologies were brought and many new are still are to be found. One such revolution was brought about by the introduction of the ‘internet’, which is till date considered as the pool of knowledge…the deeper you go in, the more you learn about your world,
about yourself.
But who could think of the time when this rich source of knowledge will be misused for criminal activities. There are many such disturbing activities that occurred in past and demanded of some rules and regulations urgently, some set definite patterns that can be put forward while carrying out any business transaction over the net, ranging from a simple friendly e-mail to carrying out the whole set of your work, without which it may go wild and beyond control and it can be used as a tool for the very destruction of mankind. It was at this point of time that the government of India felt the need to enact the relevant cyber laws which can regulate the internet in India. It denotes all aspects, issues and the legal consequences on the Internet, the World Wide Web and cyber space. Some of such laws passed are listed below:
- Information Technology Act, 2000
- Relevant Amended provisions of Indian Penal Code, 1860, Evidence Act, 1872 , Bankers Book
- Evidence Act, 1891, Reserve Bank of India Act, 1934
- IPR Laws (Copy Right Act, 1957, Patents Act, 1970, Trade Marks Act, 1999, etc)
- Right to Information Act, 2005
JURISPRUDENCE OF INDIAN CYBER LAW
The primary source of cyber law in India is the Information Technology Act, 2000 (IT Act) which came into force on 17 October 2000. Now to understand the jurisprudence of cyber law, it is essential to examine how the definitions of key terms and concepts have developed. In India the Information Technology Act, 2000 is the Mother Legislation that deals with issues related to computer systems, computer networks and the Internet.
Computer
Computer means any electronic magnetic, optical or other high-speed data processing device or system which performs logical, arithmetic, and memory functions by manipulations of electronic, magnetic or optical impulses, and includes all input, output, processing, storage, computer software, or communication facilities which are connected or related to the computer in a computer system or computer network
Data
Data means a representation of information, knowledge, facts, concepts or instructions which are being prepared or have been prepared in a formalized manner, and is intended to be processed, is being processed or has been processed in a computer system or computer network, and may be in any form (including computer printouts magnetic or optical storage media, punched cards, punched tapes) or stored internally in the memory of the computer;
Computer Software
Computer software is a general term that describes a collection of:
1. Computer programs
2. Procedures and
3. Documentation.
Computer hardware, on the other hand, consists of the physical devices that can store and execute
computer software.
Computer System
Computer system means a device or collection of devices, including input and output support devices and excluding calculators which are not programmable and capable of being used in conjunction with external files, which contain computer programs, electronic instructions, input data and output data, that performs logic, arithmetic, data storage and retrieval, communication control and other functions.
Computer Network
Computer network means the interconnection of one or more computers through:
- The use of satellite, microwave, terrestrial line or other communication media and
- Terminals or a complex consisting of two or more interconnected computers whether or not the interconnection is continuously maintained.