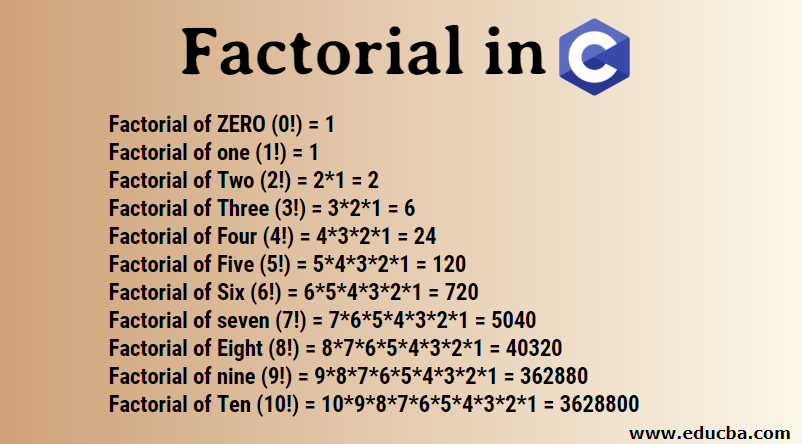
Program to find Factorial of a Number using Recursion
Program to find Factorial of a Number using Recursion #include<stdio.h> // declaring the function int fact(int); int main() { printf(“\n\n\t\tEduguru – Recursion Program Example\n\n\n”); int num, f; printf(“\n\nEnter a number: “); scanf(“%d”, &num); f= fact(num); printf(“\n\nFactorial of %d is %d\n\n”, num, f); printf(“\n\n\t\t\tCoding is Fun here !\n\n\n”); return 0; } int fact(int aj) { if(aj==1 … Read more