What is Jenkins, feature, and function of Jenkins
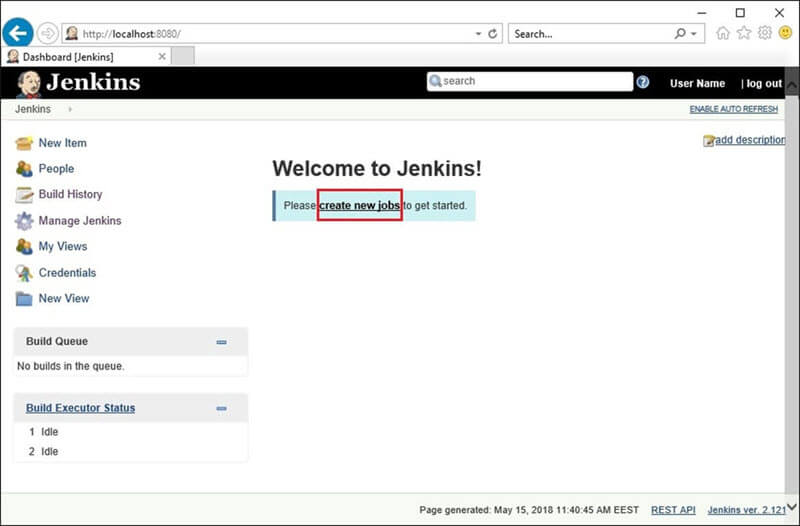
Today, We will learn What is Jenkins, the features of Jenkins, and their feature? Jenkins is an award-winning continuous integration tool that monitors executions of deployment cycles. It started as a side project by Sun’s software engineers group. Later it was expanded as one of the popular open-source CI tools which help software development teams to automate … Read more