SELinux : Introduction to SELinux
SELinux, or Security-Enhanced Linux, is a part of the Linux security kernel that acts as a protective agent on servers.
In the Linux kernel, SELinux relies on mandatory access controls (MAC) that restrict users to rules and policies set by the system administrator.
MAC is a higher level of access control than the standard discretionary access control (DAC), and prevents security breaches in the system by only processing necessary files that the administrator pre-approves.
History of SELinux
SELinux was initially released as a collaborative between Red Hat and the National Security Agency.
SELinux receives periodic updates and additions as new Linux distributions are released.
The SELinux kernel separates policy and decisions inside the kernel to distribute levels of protection and prevent a total security breach.
SELinux acts under the least-privilege model. SELinux only grants access if the administrator writes a specific policy to do so.
Why do we need SELinux?
Enabling SELinux helps reduce risk of harm to applications and other user programs. It helps prevent malicious or poorly written programs from doing harm to the overall system.
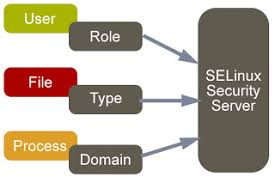
The essence of SELinux is the access controls, integrity controls, role-based access controls (RBAC) and type enforcement architecture.
Use of SELinux
SELinux provides a flexible Mandatory Access Control (MAC) system built into the Linux kernel. Under standard Linux Discretionary Access Control (DAC), an application or process running as a user (UID or SUID) has the user’s permissions to objects such as files, sockets, and other processes.
What does SELinux enforcing mean?
An SELinux-hardened system will run with SELinux in enforcing mode, meaningthat the SELinux policy is in effect and things that it doesn’t want to allow won’t be allowed. But when trying to debug permission problems, it might make sense to temporarily disable SELinux.
How do I turn off SELinux?
To temporarily disable SELinux (until reboot), use the setenforce 0 command. To disable SELinux permanently, follow these steps: Open the /etc/selinux/config file in a text editor and locate the line starting with SELINUX= . Change the line toSELINUX=disabled and save the file.
Why Selinux to be disabled?
Some of the module would not load on Enabled Selinux. So we use to disable the SELinux.
How do I disable Selinux?
Disable SELinux in Linux
- Use the graphical interface to disable SELinux while you configure your operating system, and then reboot the server.
- Edit the /etc/selinux/config file to set the SELINUX parameter to disabled , and then reboot the server.

SELinux modes
There are three modes of SELinux: Enforcing, Permissive and Disabled.
- Enforcing mode is the default mode at installation of SELinux. It will enforce the policies on the system, deny access and log actions.
- Permissive mode is the most commonly used mode for troubleshooting SELinux. In this mode, SELinux enables but does not enforce security policies. Also, this means that actions will result in a warning and log for the system administrator.
- Disabled mode means that SELinux is turned off and the security policies do not protect the server.