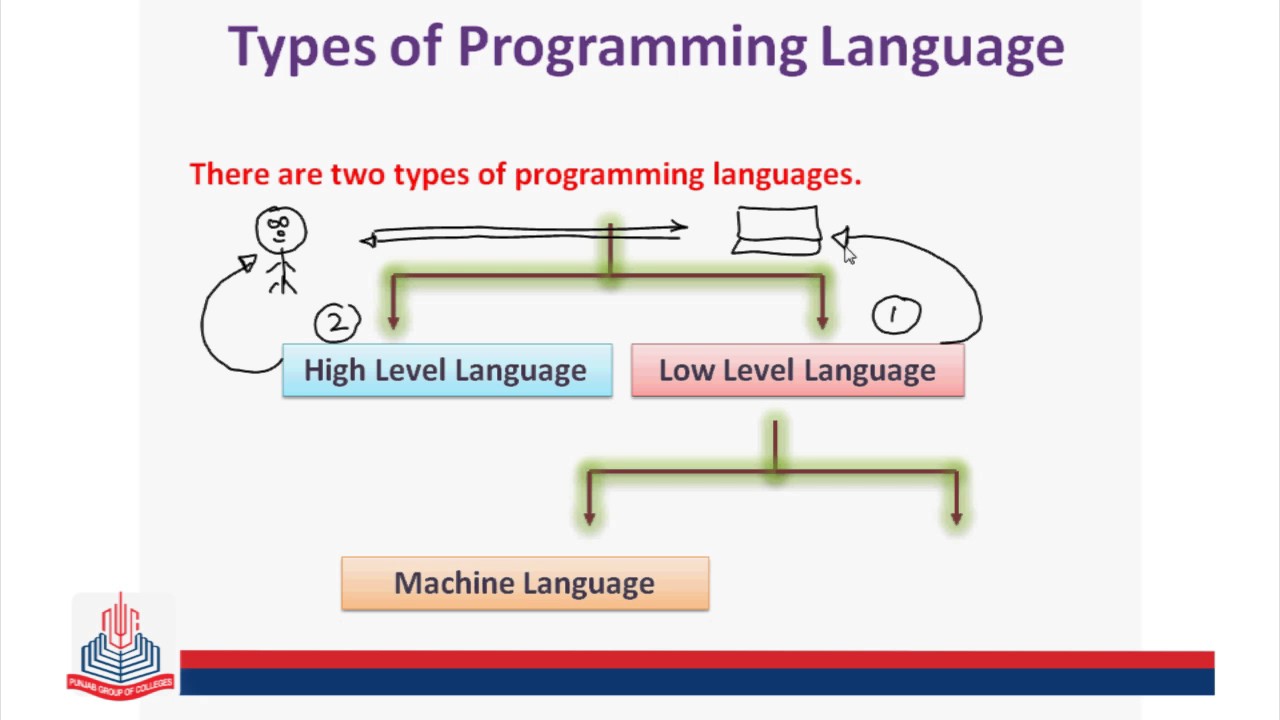
Types of programming languages
Programming languages A programming language is a means of communication for the user to communicate with the computer system. The programming language is a set of instructions which tells the computer what to do. This is a language which is understood by both man and machine. There are a number of programming languages. However all … Read more